The Security Agent in Action
Simply prompt the agent in natural language to trigger deep, cross-platform audits using our proprietary Graph Engine.
Automate compliance with our proprietary Plug & Play Security Agent. No complex setup—just enterprise-grade intelligence in a single command.
Simply prompt the agent in natural language to trigger deep, cross-platform audits using our proprietary Graph Engine.
Integration debt kills SaaS valuation. ReguLens AI eliminates it. Our engine is packaged as a lightweight Docker container, allowing teams to "Plug & Play" into any cloud environment without installing intrusive agents on local servers.
No custom code required. Deploy into your existing CI/CD pipeline in under 60 seconds.
Deliver full compliance gap analysis (SOC2/GDPR) within the first 5 minutes of activation.
$ docker pull regulens/ai-agent:latest
Pulling compliance intelligence engine...
$ docker-compose up -d
[SUCCESS] Network regulens-ai_default
[SUCCESS] Container regulens-ai-frontend-1
[SUCCESS] Container regulens-ai-api-1
_
Engineered for Hyper-Growth
Built with a high-performance, modern stack designed for asynchronous multi-cloud concurrency and agentic intelligence.
We don't just sell the code; we ensure the success of the transition. Our IP transfer comes with guaranteed technical stewardship.
Full technical handover and support for 6 months after acquisition. We guarantee a 100% bug-free transition of all Dockerized environments.
Ready-to-deploy modules for scanning **AWS Instances** and **Managed Databases (RDS)**. Custom scanning logic can be tailored to meet high-ticket client requirements.
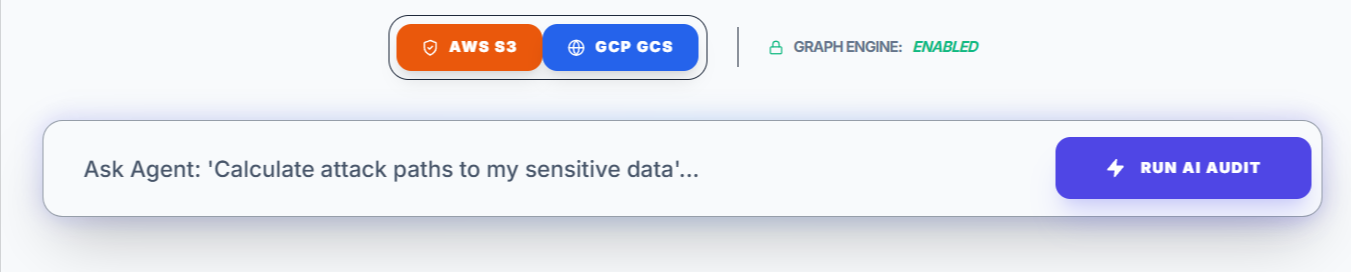
ReguLens AI bridges the gap between AWS and GCP. Our Infrastructure Discovery interface provides a unified entry point to link your credentials. Once connected, our agentic AI autonomously discovers every storage bucket, compute instance, and IAM role across your entire global footprint.
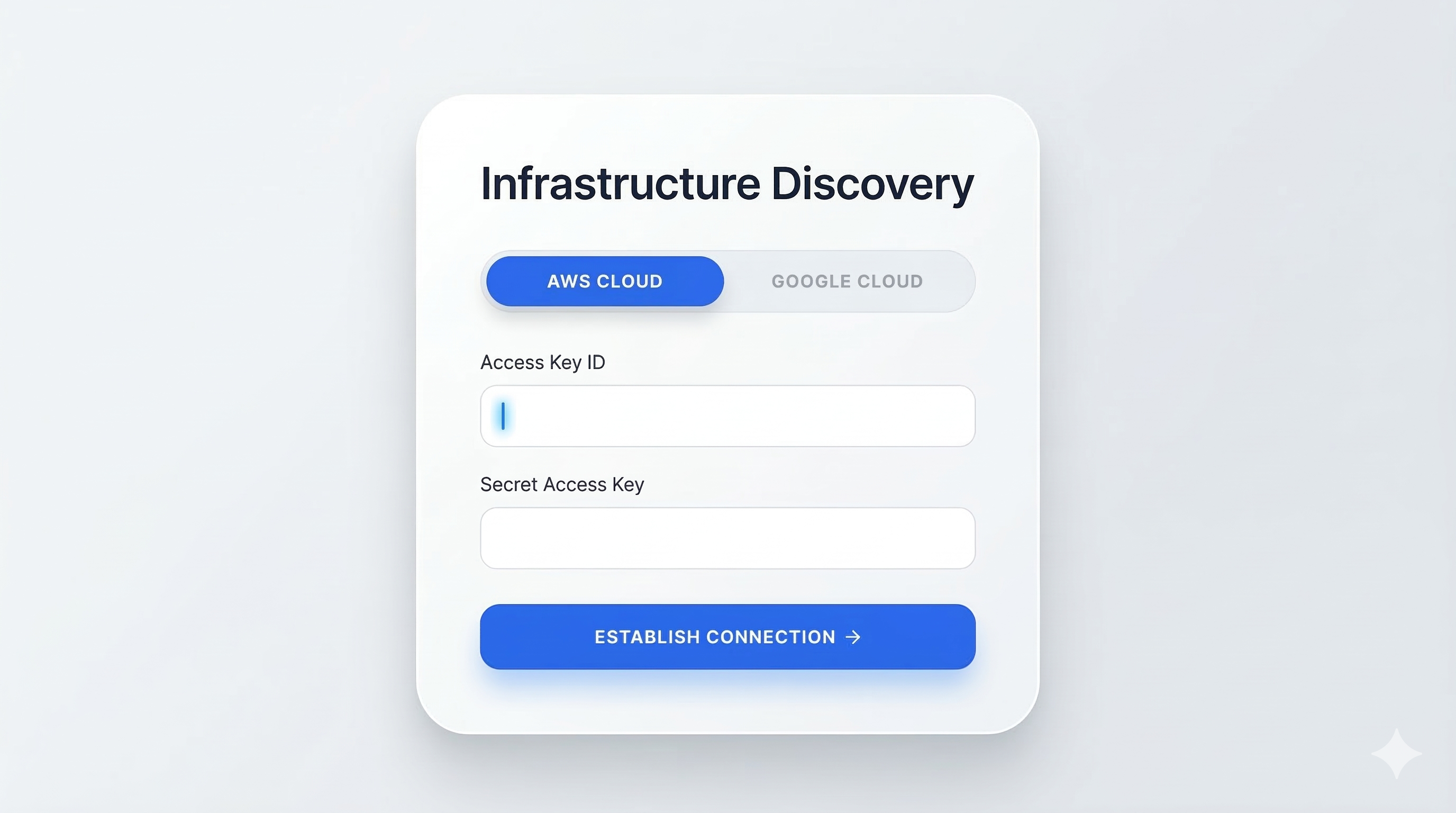
Graphs are superior to lists. They reveal the context of a threat. By visualizing your infrastructure as a graph, ReguLens AI identifies "hidden paths" an attacker would take to reach your data.
An attacker can bypass internal controls via direct requests to storage endpoints. Because these buckets are public, no lateral movement is required—the sensitive data is exposed at the storage layer as identified in the AI Attack Vector Analysis.
"The environment is facing a massive, multi-cloud data exposure event. Multiple AWS S3 and GCP buckets contain sensitive backup data accessible directly from the public internet."
Step-by-step instructions to eliminate critical vulnerabilities.
Found on: AWS S3 (Finance-Backups), GCP (Customer-Assets). These were flagged in the discovery scan.
Keys older than 90 days detected across 4 AWS users. Automation suggested via CI/CD.
Generate cryptographically verified compliance reports instantly based on your discovery and analysis results.
Clean, professional formatting for executive stakeholders and regulatory auditors.
Raw data for developer ingestion and real-time SIEM tool integration.
4+
CORES
8GB
RAM
ONNX
ENGINE
DOCKER
READY